
Little Snitch 3 your network connection monitor
I have a couple of applications that I always install on a new Mac. Little Snitch 3 is one of them. They are the essential software I need to have installed to be productive and secure. Little Snitch by Objective Development is one of them. I’ve been using it for more than ten years now, and I wouldn’t dream of running a Mac without it installed. What Little Snitch 3 essentially does is monitor all outgoing traffic from your open applications and processes and gives you the ability to allow or deny that traffic. It is an excellent way of seeing what kind of information is sent from applications without your knowledge or consent. And it’s a great way of stopping traffic that “Phones home” without your explicit permission. When an application tries to send out something over the network, it gets intercepted by Little Snitch, and you can then allow or deny the connection, either temporary or permanently via the dialog box that appears. So Little Snitch is always there, protecting your privacy.
Deny or Allow?
When an application tries to connect, and if you haven’t already set up a rule, you’ll get this dialog box automatically.
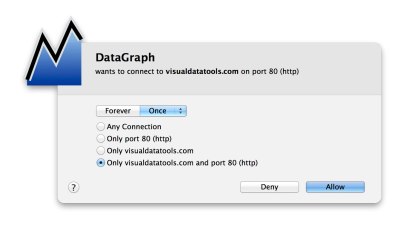
As you can see, you can choose “Deny” or “Allow” if it should be denied or allowed forever or one of the following choices: 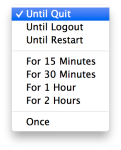 So you could let an application make the connection until you quit the app, or for a finite time, like 1 hour. For me, it’s almost always Forever or Once. After you have selected your parameters, press Deny or Allow and Little Snitch 3 will guard you against that traffic, allowing or denying the traffic depending on your settings. This is incredibly handy. As you can see in the dialog box, you can force the application to be allowed or denied for a specific port, a particular domain name or port, and domain name. This is great if you want to be sure that the application doesn’t connect to any other place using another protocol. So you have fine-grained control over the communications going out from the app.
So you could let an application make the connection until you quit the app, or for a finite time, like 1 hour. For me, it’s almost always Forever or Once. After you have selected your parameters, press Deny or Allow and Little Snitch 3 will guard you against that traffic, allowing or denying the traffic depending on your settings. This is incredibly handy. As you can see in the dialog box, you can force the application to be allowed or denied for a specific port, a particular domain name or port, and domain name. This is great if you want to be sure that the application doesn’t connect to any other place using another protocol. So you have fine-grained control over the communications going out from the app.
Editing The Rules
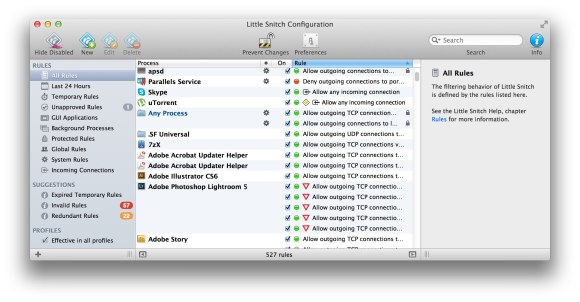
You can quickly change the rules you have configured by selecting “Rules…” in the Little Snitch 3 menu bar. Here you can add or remove rules or do changes.
Invalid Rules
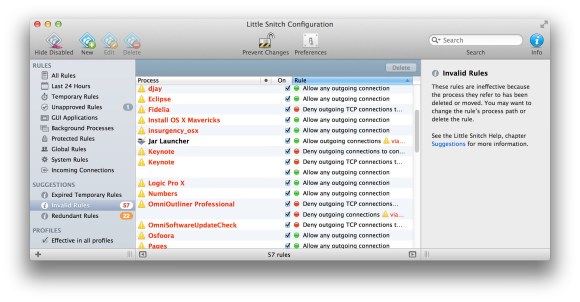
In the left column of the main window, you have something called Invalid Rules. Here you see rules that don’t apply anymore because the application in question no longer exists or changed name. It’s smart to go through this list once in a while to keep the Little Snitch 3 rules lean and clean.
Redundant Rules
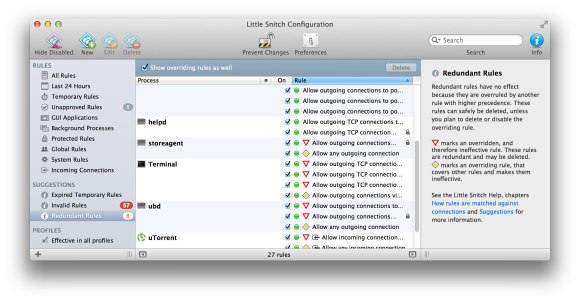 This selection shows rules that override each other. It makes it easy to clean up redundant rules. You can go through the rules and remove unnecessary ones, like when one rule invalidates another, etc.
This selection shows rules that override each other. It makes it easy to clean up redundant rules. You can go through the rules and remove unnecessary ones, like when one rule invalidates another, etc.
Network Monitor Window
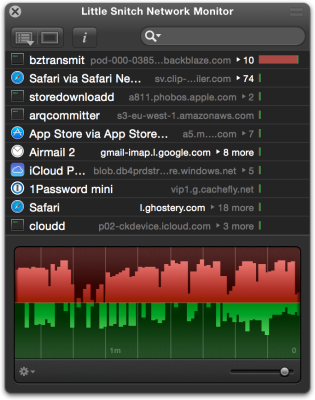
There’s a network monitor window that you can use to see all the in and outgoing traffic. You can sort the data in the window after:
- Last activity
- Traffic Amounts
- Process
- Hostname
So this is an excellent tool to find applications that hog the internet connection for example.
I think it’s great being able to have complete control over what and where my applications can do. There’s probably a lot of people who use it for pirated software, so the app doesn’t phone home, but that’s not my reason for using it. I want to see if any process on my computer tries to connect somewhere without my permission and to use the Research Assistant that gives more information about the specific traffic. It would be extra hard for a Trojan to try to do something without me knowing either, so that’s another benefit.
Automatic Profile Switching
New in version 3 is Automatic Profile Switching. When you switch between networks, like home and work, for example, Little Snitch 3 can automatically change rules. So you could ban all traffic to FaceBook at work, or allow traffic you wouldn’t allow at home. I haven’t tried this feature but will soon.
Gary J says
what to the red and yellow triangles mean when looking at the rules?
Jack Zimmermann says
They indicate that there are other rules that are in effect, overruling it. Red usually signifies rules for applications no longer installed.